From Niche to Necessity: Key Catalysts Behind OT Security Market Growth
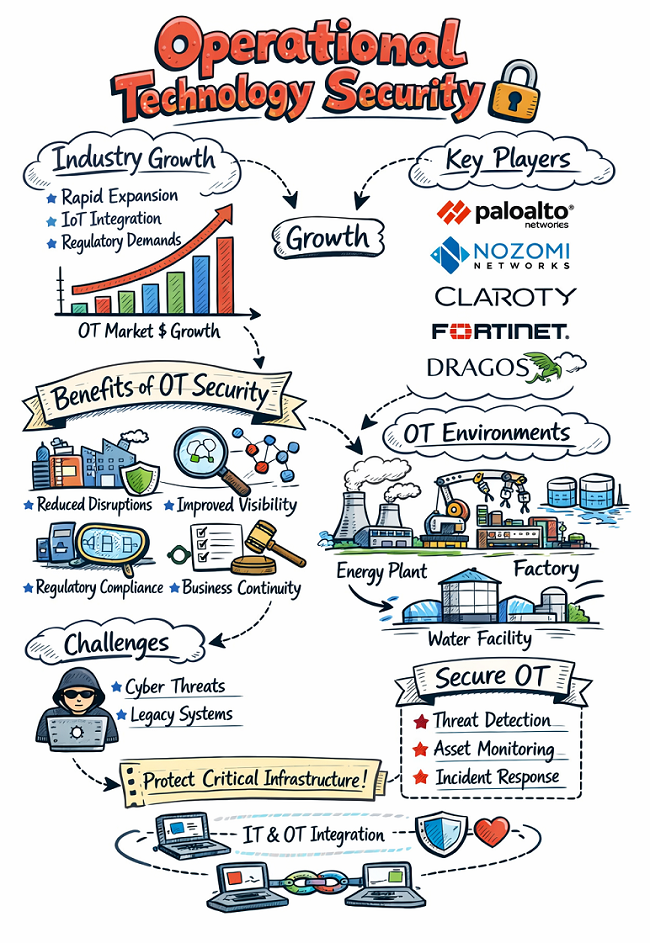
The market for Operational Technology (OT) security is currently experiencing a period of explosive, unprecedented expansion, transforming it from a niche concern into a C-suite and national security priority. This surge is not driven by a single factor but by a powerful confluence of trends, with the primary catalyst being the widespread digital transformation and IT/OT convergence. The relentless pursuit of efficiency, predictive maintenance, and data-driven insights—the cornerstones of Industry 4.0—has led organizations to connect their once-isolated industrial control systems to IT networks and the cloud. While this has unlocked immense business value, it has also shattered the "air gap" myth, exposing sensitive operational environments to the full range of internet-borne threats. This convergence has created a massive new attack surface, and the urgent need to secure it is the fundamental driver behind the incredible Operational Technology Security Market Growth. Organizations now realize that the same network that processes their emails is connected, often just a few hops away, to the systems that control their physical processes, making OT security an unavoidable necessity.
A second and equally powerful driver of market growth has been the dramatic and highly publicized nature of recent OT cyberattacks. While the Stuxnet worm in 2010 was an early wake-up call, the 2021 ransomware attack on the Colonial Pipeline was a watershed moment that brought the vulnerability of critical infrastructure into the public consciousness and the boardroom. The attack, which originated in the IT network, led to the precautionary shutdown of the largest fuel pipeline in the United States, causing widespread panic and economic disruption. This incident demonstrated, in no uncertain terms, the real-world kinetic consequences of a cyberattack. Similarly, the TRITON/TRISIS malware, specifically designed to manipulate industrial safety systems, raised the terrifying specter of attacks intended to cause physical destruction and loss of life. These high-profile events have fundamentally shifted the risk calculation for boards of directors and government leaders, transforming OT security from a theoretical risk into a clear and present danger that demands immediate and substantial investment.
The third major accelerator of OT security market growth is the rapidly escalating regulatory landscape. Governments around the world, having witnessed the devastating potential of attacks on critical infrastructure, are no longer content to let industries police themselves. In the United States, the Transportation Security Administration (TSA) has issued security directives for pipeline operators, and regulatory frameworks like the North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) standards for the power sector are becoming stricter and more prescriptive. In Europe, the Network and Information Security (NIS2) Directive has significantly expanded the scope of industries deemed "essential" and has imposed stringent cybersecurity requirements, including heavy fines for non-compliance. This wave of regulation is creating a powerful compliance-driven market. Organizations are now legally and financially compelled to invest in OT security solutions, not just as a best practice, but as a mandatory requirement to continue operations, providing a sustained and predictable driver for market growth.
Finally, the increasing sophistication of adversaries is a constant and escalating driver. Nation-state actors and organized cybercriminal groups have recognized the immense strategic and financial leverage that can be gained by targeting critical infrastructure. Ransomware gangs have discovered that threatening the operational uptime of a manufacturing plant or a utility is far more lucrative than encrypting files on a corporate server. State-sponsored groups are actively pre-positioning themselves within critical infrastructure networks for potential future geopolitical conflicts. This professionalization of the threat landscape means that OT environments are no longer just accidental victims of IT malware; they are now specific, intentional targets. The need to defend against these well-funded and highly skilled adversaries is forcing organizations to abandon their legacy security postures and invest in the advanced, purpose-built OT security technologies and expertise necessary to detect and respond to these modern threats, ensuring the market's continued upward trajectory.
Explore More Like This in Our Reports:
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Jocuri
- Gardening
- Health
- Home
- Literature
- Music
- Networking
- Alte
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness